Our Blog
Latest news and updates from HostAsean
XMLRPC Attacks – Secure Your WordPress Website
Posted by Mr WordPress on 11 02 2016. in Coding & Web Development, Website Security, WordPress

Recently we have noticed more and more frequent attacks on the xmlrpc.php file in WordPress, this can cause a number of problems for a website owner from resource usage up to malicious hacking attempts to gain access to the website or data. So how to keep your website security strong and stop these attacks?
The xmlrpc.php file contains a function that enables external apps to communicate with and post to your WordPress site on your behalf, it has been there for a while but most people don’t use this functionality.
If I don’t use xmlrpc, can I delete it?
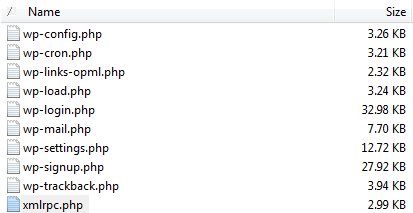
You can just delete or rename the xmlrpc.php file in your FTP client.
Attacks on xmlrpc.php can be simply DoS attacks that overuse resources, bringing your site to a crawl or making it completely unavailable. This is the equivalent of many visitors hitting your site all at once. The attack can have a more sinister intention though, as the xmlrpc interface enables hackers to try multiple usernames and password attempts, bypassing the wp-login.php file.
On the HostAsean hosting servers we monitor and check for excessive resource usage by xmlrpc.php and any other files or scripts. Since removing the file on a number of our customer’s websites we have noticed that these have completely stopped, as there is now no file for the attacks to hit and therefore no vulnerability. As a bonus, by preventing so many attempted attacks by removing the files it reduces the load on the entire server. This should give everyone hosted with us a faster website.
You might see a message like this if you run “lfd”, removing xmlrpc.php will stop these notifications:
Suspicious process running under user username Time: Mon Jan 25 04:50:26 2016 +0700 PID: 17515 (Parent PID:27615) Account: username Uptime: 110 seconds Executable: /usr/bin/php Command Line (often faked in exploits): /usr/bin/php /home/username/public_html/xmlrpc.php Network connections by the process (if any): tcp: 11.222.333.444:42407 -> 1111.222.333.444:443
There is one thing to note, and the API is required if you use the Jetpack plugin, or other external apps to access or post to your WordPress site. It is possible to block xmlrpc but still allowing access from Jetpack/Automattic servers to allow these trusted plugins to function. It is otherwise completely safe to delete the xmlrpc.php file, but if you find that you do need it – it can be restored easily by just downloading a copy of the WordPress core files from www.wordpress.org and re-uploading the file again.
If you have a WordPress website hosted with us, we would be happy to close this vulnerability to help secure your website. Just contact support@nullhostasean.com and let us know what your domain name is and we’ll remove the file for you.
 ASEAN / Global
ASEAN / Global Cambodia
Cambodia